The Best of Mitigant Blog Articles in 2023


True to our passion at Mitigant, we shared lots of original knowledge on our blog this year. A total of fifteen blog posts were published, almost twice as many as last year. This was the first full year of the blog's existence. Interestingly, most blog articles spawned from expressions of our mission and interactions with stakeholders (awesome customers, investors, advisors, and communities we are involved in).
For the sake of context, you need to understand the products we were building since most discussions revolved around them. We started the year with a single product: Cloud Security Assessment (CSA), an innovative Cloud Security Posture Management (CSPM) product. Mitigant CSA was released last year in August with support for AWS, and support for Azure was added in May this year. During this year, two additional products were added to the Mitigant cloud security platform: Cloud Immunity and Kubernetes Security Posture Management (KSPM).
Now, let me highlight this year's top ten most performant blog articles.
1. Security Chaos Engineering 101: Fundamentals
This article discusses the positioning of Security Chaos Engineering (SCE) as an aspect of security engineering. The primary motivation is to allow security engineers and other cyber-security professionals to view SCE as an integral aspect of security engineering, not an esoteric craft. Adopting this mindset is vital for demystifying SCE and gaining its inherent benefits. Furthermore, two misconceptions about SCE are addressed in this article to present objective information and clarity of knowledge. Read the complete article here.

2. Leveraging Security Chaos Engineering for Cloud Cyber Resilience - Part I
This blog discusses some challenges to adopting practical cyber resilience. It provides insights into how security chaos engineering wields game-changing opportunities for adopting empirical cyber resilience.
Read the complete article here.

3. Security Chaos Engineering 101: Getting Your Hands Dirty
This article follows an earlier article in which several aspects of SCE were discussed, including some common misconceptions. In this article, practical examples of conducting SCE experiments are provided.
Read the complete article here.

4. Supercharging Cloud Detection & Response With Security Chaos Engineering
Effective Cloud Detection & Response (CDR) strategies are imperative for promptly identifying and responding to cloud security events. However, enabling efficient CDR strategies is challenging for several reasons, including cloud complexities, insufficient expertise, and cloud misconfiguration. This article makes a case for leveraging security chaos engineering to address these challenges. Defenders can leverage security chaos engineering for threat-hunting efforts to identify CDR blindspots proactively. Some practical examples are illustrated using Mitigant Cloud Immunity and a hybrid CDR system.
Read the complete article here.

5. Cloud Attack Emulation: Enhancing Cloud-Native Security With Threat-Informed Defense
Speed and agility are essential for effectively achieving cybersecurity goals in this cloud-native era. High-performing engineering teams leverage modern infrastructure and technology to increase deployment velocity and capability to react to adverse changes. Cyber security is no different; agility is even more critical since detection and response to adverse conditions are often time-sensitive, especially in the face of adversity. Accordingly, cloud security teams must leverage agile and proactive approaches and implement Threat-Informed Defense mechanisms. One of these approaches is cloud attack emulation, an emerging methodology that allows quick validation of security goals by mimicking adversarial behavior.
This article discusses cloud attack emulation and its advantages and demonstrates an actual use case scenario involving the AndroXGh0st malware.
Read the complete article here.

6. Leveraging Security Chaos Engineering for Cloud Cyber Resilience - Part II
The first part of this blog series discussed the difference between cyber resilience and cyber security and decoupled the concept of cyber resilience through the lens of the people, process, and technology framework. This concluding part dives more deeply into cloud cyber resilience by examining the current state-of-the-art, highlighting cyber resilience engineering, and connecting the dots between the NIST Cyber Resiliency Engineering Framework and Security Chaos Engineering.
Read the complete article here.

7. Is Your Cloud NIS2 Ready?
Ensuring the cloud is secure, compliant, and resilient is one of the responsibilities of cloud customers. One of the upcoming legislations enforced in 2024 is the European Union’s Network and Information Systems 2 (NIS2) Directive, Europe's most comprehensive cybersecurity legislation. This blog post provides an overview of the NIS2 Directive, how it could affect you and your cloud, and how to prepare for it.
Read the complete article here.

8. CIS Benchmarks for Cloud Infrastructure Security Compliance
You have probably seen or read the term CIS benchmarks when searching for cloud security compliance online. CIS benchmark is recognized as one of the market's popular cloud security best practices and standards. Still, what are CIS benchmarks, and does your cloud infrastructure need to comply with them? This blog post will overview the CIS benchmarks and how they can be used for cloud infrastructure security and compliance.
Read the complete article here.

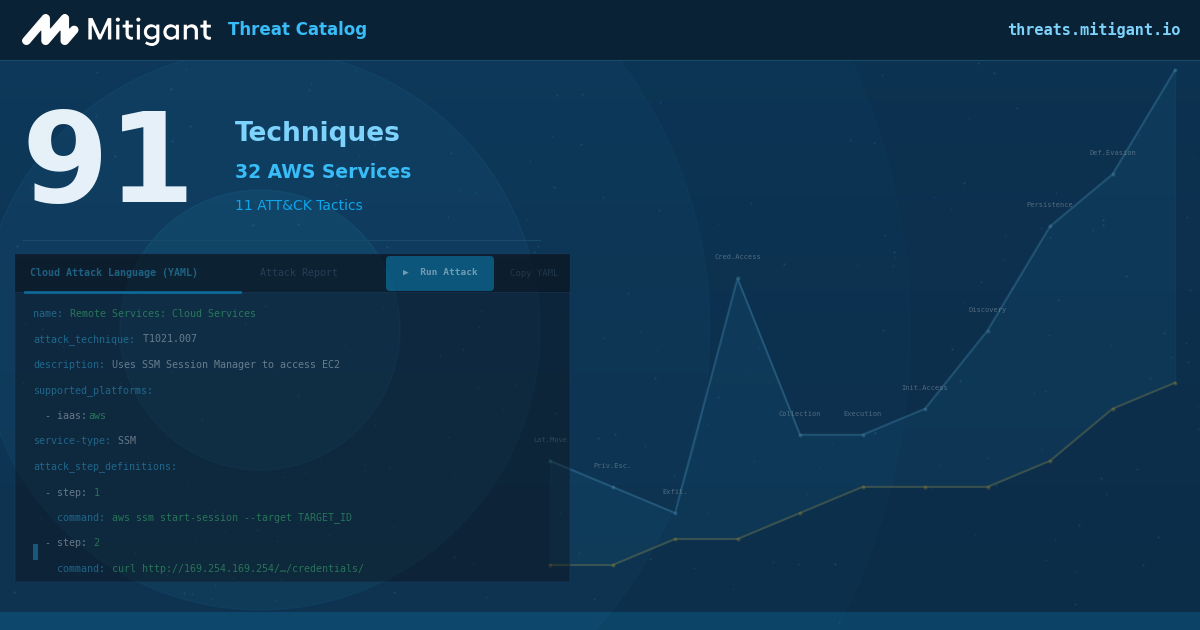
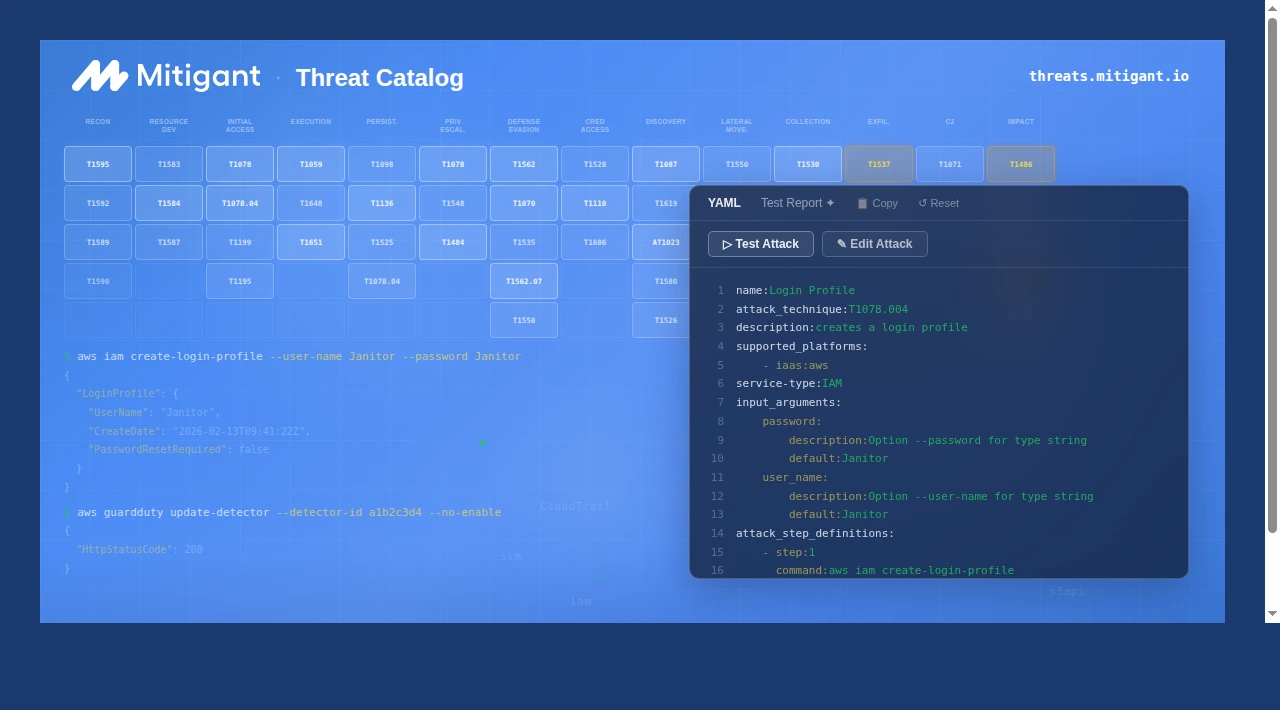
9. Public Release - Mitigant Security Chaos Engineering SaaS
We proudly released the world’s first implementation of Security Chaos Engineering as a SaaS product. The release blog article discussed the motivation behind building the product and the features that were part of the release. More features have been added since then.
Read the complete article here.

10. Security Chaos Engineering 101: The Mind Map & Feedback Loop
This third article in the Security Chaos Engineering 101 series discusses two important SCE concepts: the SCE mind map and the SCE feedback loop. The SCE mind map succinctly presents critical fundamental SCE information colloquially known as the what, why, who, how, and where of SCE. Conversely, the SCE feedback loop leverages the power of systems thinking to enable an objective approach to understanding and addressing cyber security and resilience challenges.
Get the full gist here.

Happy Holidays and Best of 2024!
We have a lot of even more exciting blog articles planned for 2024. If you have not noticed, we have hosted a couple of webinars, all accessible for free. Go check out the Webinar page. We also started a LinkedIn newsletter this year; you'd like to check it out and subscribe. Link here.
Enjoy the rest of the festive season, and best wishes for 2024.





.png)