Built for Security Teams at Every Stage



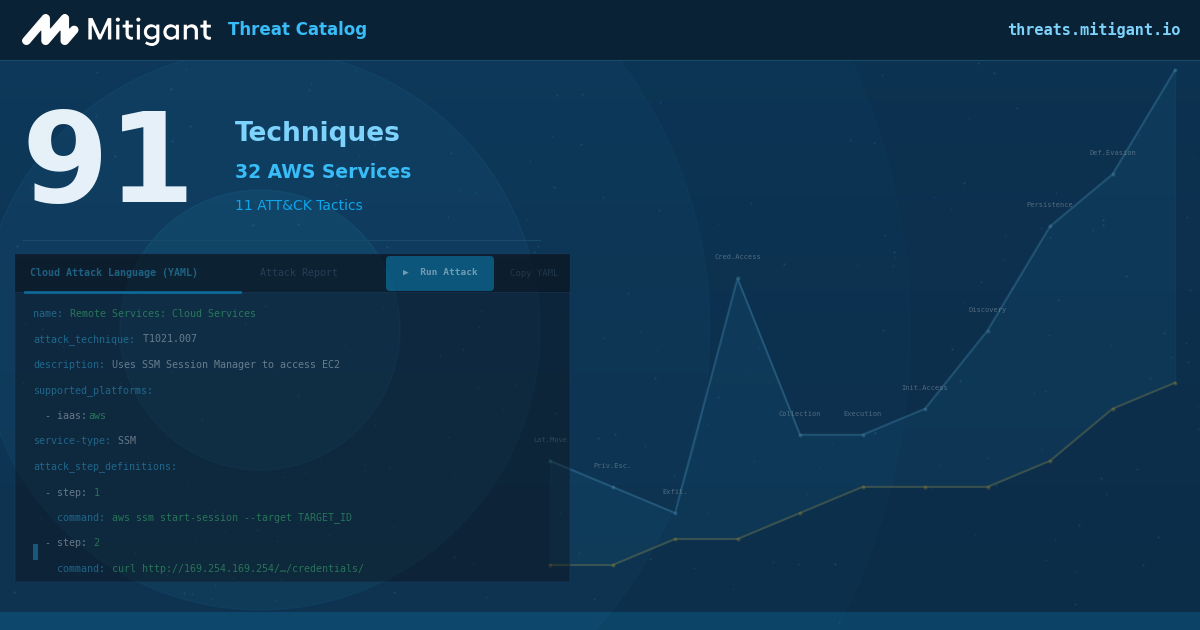
Attack Builder
Safe Attack Execution Everywhere
Attack Builder
Safe Attack Execution Everywhere
Compliance Without Guesswork
Clear Security Posture
Address Identity Risks
Attack Surface Management
Compliance Without Guesswork
Clear Security Posture
Address Identity Risks
Attack Surface Management
Continuous Compliance
Precise Vulnerability Management
Reliable Inventory Management
Continuous Compliance
Precise Vulnerability Management
Reliable Inventory Management
Seamlessly Ensure Secure and Safe GenAI Infrastructure
Cloud Immunity Use Cases


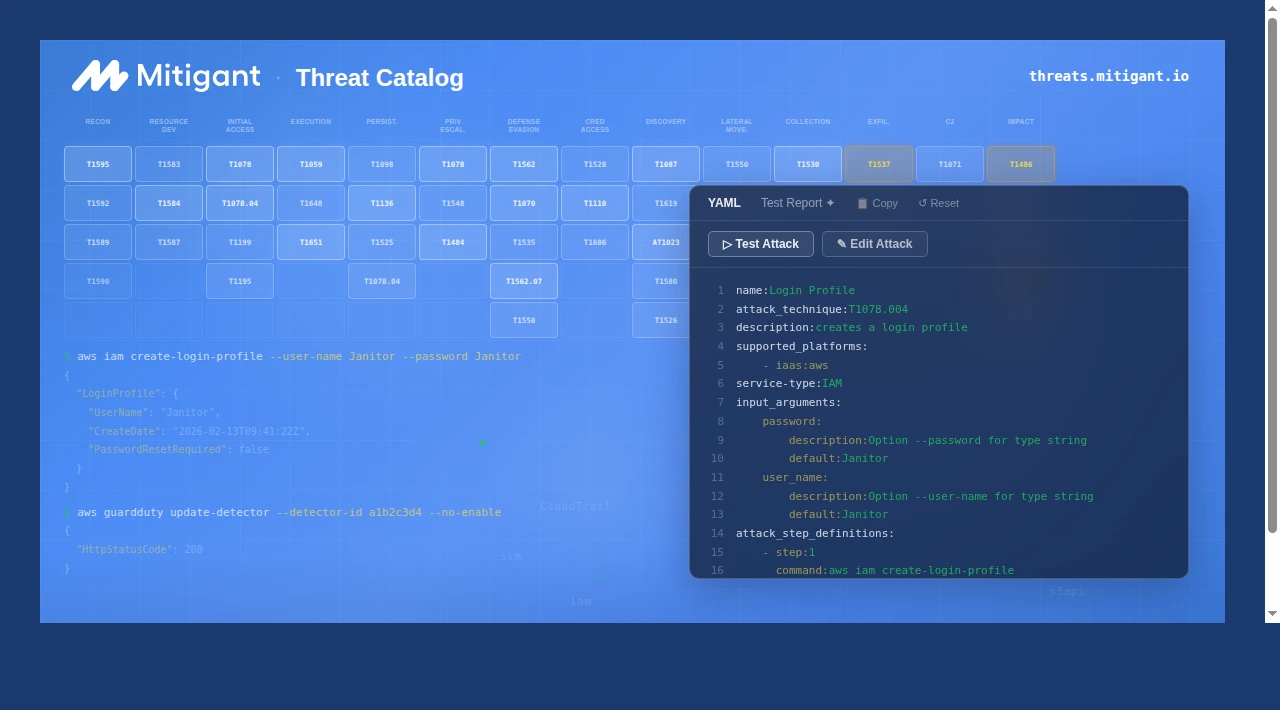
This is the original use case for cloud immunity, to make running security chaos engineering (SCE) experiments easy and straightforward. Users may define the objective of the experiment to be conducted (hypothesis); this gives a precise expectation that would define the focus of observation. The hypothesis and observation can be documented in the applications and retrieved anytime as users continue improving the security and resiliency of their infrastructure. The experiments mentioned about are implemented as attack actions and attack scenarios. Attack actions are single attacks with a single attack target, e.g., “Make an S3 bucket public”. Conversely, attack scenarios consist of two or more actions designed to present more realistic attacks, e.g., S3 Ransomware attack scenario.



This is the original use case for cloud immunity, to make running security chaos engineering (SCE) experiments easy and straightforward. Users may define the objective of the experiment to be conducted (hypothesis); this gives a precise expectation that would define the focus of observation. The hypothesis and observation can be documented in the applications and retrieved anytime as users continue improving the security and resiliency of their infrastructure. The experiments mentioned about are implemented as attack actions and attack scenarios. Attack actions are single attacks with a single attack target, e.g., “Make an S3 bucket public”. Conversely, attack scenarios consist of two or more actions designed to present more realistic attacks, e.g., S3 Ransomware attack scenario.

We Support Your Favorite Clouds












.png)