AI-Powered Cloud Adversary Emulation
Safely prove cloud exploitability with real attacks.Validate exposures, test detections, prioritize fixes.
Join security teams validating their cloud exploitability.




















Cloud Security Reality Check
Your security tools find thousands of issues. But which ones can attackers actually exploit ?
45%
of MITRE ATT&CK techniques are NOT implemented in threat detection tools
40%
of implemented MITRE ATT&CK techniques are ineffective.
3x
reduction in breach likelihood for organizations that adopt Adversarial Exposure Validation
Don't leave your security to chance. Validate what's exploitable, continuously.
The Mitigant Platform
Cloud Attack Emulation designed to safely test your defenses continuously, comprehensively, and at cloud speed.
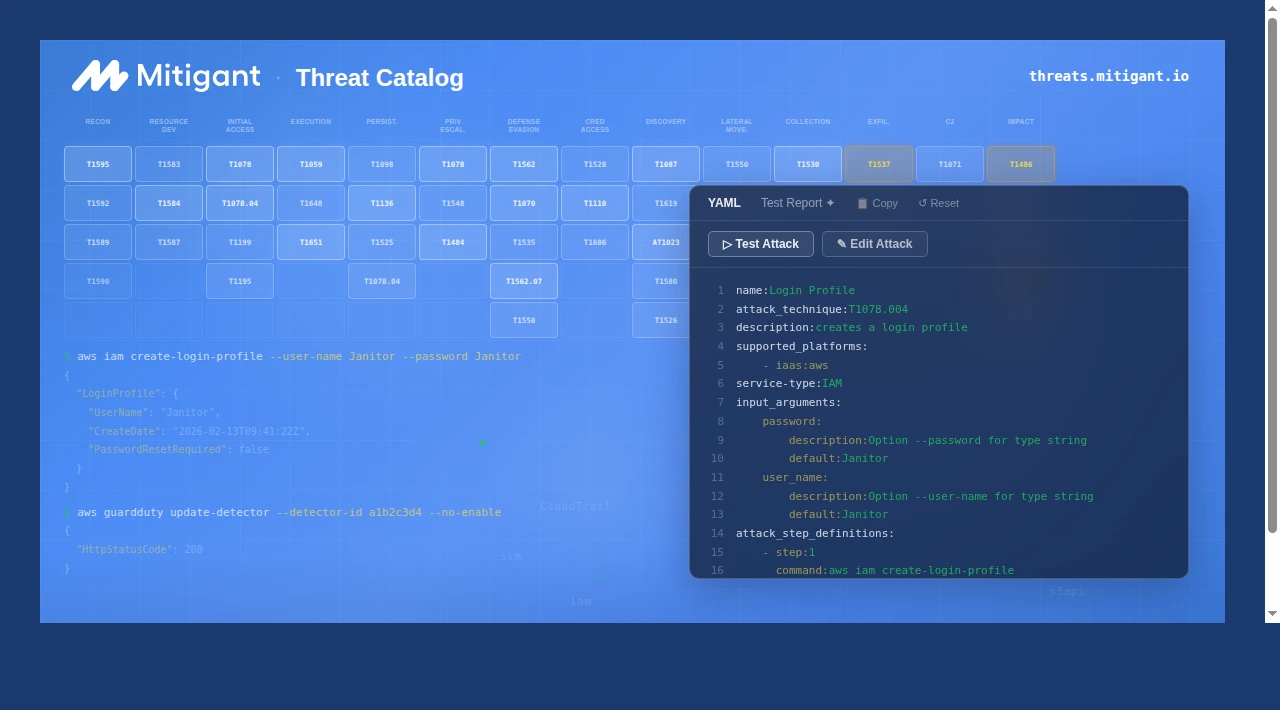
Real-World Attack Scenarios, On-Demand
Run cloud penetration testing and red/purple team exercises any time. Emulate real adversary tactics mapped to MITRE ATT&CK and MITRE ATLAS.
Leverage 250+ plug-and-play attacks across AWS, Azure, and Kubernetes. Build custom attacks with our Attack Builder using the Cloud Attack Language.
Leverage 250+ plug-and-play attacks across AWS, Azure, and Kubernetes. Build custom attacks with our Attack Builder using the Cloud Attack Language.
Learn More
Safely Validate Cloud Defenses
Safe, controlled attack emulation with built-in guardrails. Bring Your Own Role (BYOR) for precise permission control. Isolated attacks with automatic cleanup ensure no residual impact.
Validate the effectiveness of cloud detection mecahnisms. Leverage the Mitigant Attack API for agile attack orchestration. Be empowered for continuous security validation that keeps attackers out.
Validate the effectiveness of cloud detection mecahnisms. Leverage the Mitigant Attack API for agile attack orchestration. Be empowered for continuous security validation that keeps attackers out.
Learn More
AI-Powered Intelligence in Seconds
Be empowered with AI-Powered security posture analysis and precise reporting.
Understand what happened, what's exploitable, and what to fix with prioritized remediation.
Get instant actionable insights on remediation steps and hardening efforts.
Understand what happened, what's exploitable, and what to fix with prioritized remediation.
Get instant actionable insights on remediation steps and hardening efforts.
Learn More
Continuous Compliance Monitoring
Continuously monitor Cloud and Kubernetes environments for misconfigurations and compliance violations across CIS Benchmarks, NIS2, DORA, NIST, PCI-DSS, SOC 2, and more.
Keep track of cloud and Kubernetes resources with continuous asset inventory and drift management. Leverage vulnerability intelligence from EPSS and CISA KEV for effective prioritization.
Keep track of cloud and Kubernetes resources with continuous asset inventory and drift management. Leverage vulnerability intelligence from EPSS and CISA KEV for effective prioritization.
Learn More
Real-World Attack Scenarios, On-Demand
No more waiting for quarterly engagements. Run cloud penetration testing and red/purple team exercises any time, continuously. Emulate real adversary tactics mapped to MITRE ATT&CK and MITRE ATLAS, informed by Cyber Threat Intelligence.
Test AI workloads with sophisticated AI Red Teaming capabilities. Leverage 200+ plug-and-play attacks across AWS, Azure, and Kubernetes, or build custom attacks with our Attack Builder.
Test AI workloads with sophisticated AI Red Teaming capabilities. Leverage 200+ plug-and-play attacks across AWS, Azure, and Kubernetes, or build custom attacks with our Attack Builder.
Learn More
Safely Validate Cloud Defenses
Safe, controlled attack emulation with built-in guardrails. Bring Your Own Role (BYOR) for precise permission control. Isolated attacks with automatic cleanup ensure no residual impact.
Validate whether your SIEM, CDR, and cloud detection mecahnisms catch real attacks. Leverage the Mitigant Attack API and Attack-as-Code for agile attack orchestration and Detection-as-Code. Be empowered for continuous security validation that keeps attackers out.
Validate whether your SIEM, CDR, and cloud detection mecahnisms catch real attacks. Leverage the Mitigant Attack API and Attack-as-Code for agile attack orchestration and Detection-as-Code. Be empowered for continuous security validation that keeps attackers out.
Learn More
AI-Powered Intelligence in Seconds
AI analyzes your cloud posture, identifies attacks targeting your actual weaknesses, and instantly transforms the results into executive intelligence.
Understand what happened, what's exploitable, and what to fix with prioritized remediation, MITRE ATT&CK/ATLAS techniques used, and Sigma detection rules required for remediation. Instantly get easily actionable insights into multi-step and multi-cloud attacks and operate with agility.
Understand what happened, what's exploitable, and what to fix with prioritized remediation, MITRE ATT&CK/ATLAS techniques used, and Sigma detection rules required for remediation. Instantly get easily actionable insights into multi-step and multi-cloud attacks and operate with agility.
Learn More
Continuous Compliance Monitoring
Continuously monitor Cloud and Kubernetes environments for misconfigurations and compliance violations across CIS Benchmarks, NIS2, DORA, NIST, PCI-DSS, SOC 2, and more.
Keep track of cloud and Kubernetes resources with continuous asset inventory and drift management. Leverage vulnerability intelligence from EPSS and CISA KEV for effective prioritization.
Keep track of cloud and Kubernetes resources with continuous asset inventory and drift management. Leverage vulnerability intelligence from EPSS and CISA KEV for effective prioritization.
Learn More

Solutions for Every Cloud Security Challenge
Six purpose-built solutions to strengthen your cloud security posture.
AI Red Teaming
Purpose-built for testing AI workloads in the cloud.

Cloud Penetration Testing
Streamlined cloud penetration testing, no need to wait for months!

Detection Validation
Prove your defenses actually work as desired.

SOC Team Optimization
Give your SOC team their time back, so they focus on the more important stuff.

Continuous Compliance
Stay audit-ready, always; no longer a point in time.

Incident Readiness
Practice makes perfect; ensure your incident response processes function effectively.

Trusted by Security Leaders

Jendrik Jordening
CTO, Nooxit

We were able to spin up Mitigant in a day. Reproducibly pushing it through dev and stage into prod, because of its easy-to-use helm chart and plug-and-play abilities. The reports were generated swiftly and gave us great points to work from to increase and test our existing security measures and tools

Devin Lemcke
Co-Founder, Notch

The services we offer at Notch often require interaction with enterprise systems; therefore security and privacy are important for us. Mitigant is the right solution for us, it enables quick and continuous visibility into our cloud security and complaince posture. This saves us time, effort, and cost, allowing us to remain agile and focused on our core business goals.

Daniel Sarosi
Technology Platform Lead, KM.ON Asia Ltd

Before working with Mitigant, managing the security of KM.ON’s cloud infrastructure and Kubernetes environments were challenging. Traditional security tools did not address the scale and agility required in the cloud-native environment. Mitigant’s Cloud Security Platform provides deep and clear visibility of KM.ON’s cloud workloads. I am thrilled with the outcome of the Mitigant Cloud Security Platform.

Ramon Kania
CTO, Mitto

Cloud security is an important aspect of the service we provide for our customers. However, due to the fast-paced evolution of cloud infrastructure, keeping a secure cloud infrastructure becomes quite tricky. By leveraging the Mitigant CSPM, we address these challenges by enabling a continuously dependable cloud security posture.

Stephan Häußler
CTO, Adair

Signing up to the Mitigant CSPM was seamless and fast, it took barely 15 minutes for me to clearly see the security issues in my AWS cloud account. As a startup founder, using Mitigant saves me a lot of time and enables me to focus on my core business objective.

Markus Guerster
CEO, MontBlancAI

Signing up to the Mitigant CSPM for Azure was seamless and fast. It took barely 10 minutes to get a very clear representation of our Azure security posture. As a startup founder, using Mitigant gives me a big confidence boost that we are doing the right things to keep our customers’ data secure while maintaining agility.

Charles Nwatu
Cyber Security Executive & Security Chaos Engineering Pioneer
Security Chaos Engineering is vital in helping organizations understand how resilient they are to security and technology disruptions. Mitigant turns Security Chaos into Clarity. Mitigant informs the business where it can invest its resources.

Jendrik Jordening
CTO, Nooxit

We were able to spin up Mitigant in a day. Reproducibly pushing it through dev and stage into prod, because of its easy-to-use helm chart and plug-and-play abilities. The reports were generated swiftly and gave us great points to work from to increase and test our existing security measures and tools

Devin Lemcke
Co-Founder, Notch

The services we offer at Notch often require interaction with enterprise systems; therefore security and privacy are important for us. Mitigant is the right solution for us, it enables quick and continuous visibility into our cloud security and complaince posture. This saves us time, effort, and cost, allowing us to remain agile and focused on our core business goals.

Daniel Sarosi
Technology Platform Lead, KM.ON Asia Ltd

Before working with Mitigant, managing the security of KM.ON’s cloud infrastructure and Kubernetes environments were challenging. Traditional security tools did not address the scale and agility required in the cloud-native environment. Mitigant’s Cloud Security Platform provides deep and clear visibility of KM.ON’s cloud workloads. I am thrilled with the outcome of the Mitigant Cloud Security Platform.

Ramon Kania
CTO, Mitto

Cloud security is an important aspect of the service we provide for our customers. However, due to the fast-paced evolution of cloud infrastructure, keeping a secure cloud infrastructure becomes quite tricky. By leveraging the Mitigant CSPM, we address these challenges by enabling a continuously dependable cloud security posture.

Stephan Häußler
CTO, Adair

Signing up to the Mitigant CSPM was seamless and fast, it took barely 15 minutes for me to clearly see the security issues in my AWS cloud account. As a startup founder, using Mitigant saves me a lot of time and enables me to focus on my core business objective.

Markus Guerster
CEO, MontBlancAI

Signing up to the Mitigant CSPM for Azure was seamless and fast. It took barely 10 minutes to get a very clear representation of our Azure security posture. As a startup founder, using Mitigant gives me a big confidence boost that we are doing the right things to keep our customers’ data secure while maintaining agility.

Charles Nwatu
Cyber Security Executive & Security Chaos Engineering Pioneer
Security Chaos Engineering is vital in helping organizations understand how resilient they are to security and technology disruptions. Mitigant turns Security Chaos into Clarity. Mitigant informs the business where it can invest its resources.
Join The Cloud Security Revolution Today!
Take control of your cloud security in minutes. No credit card required.