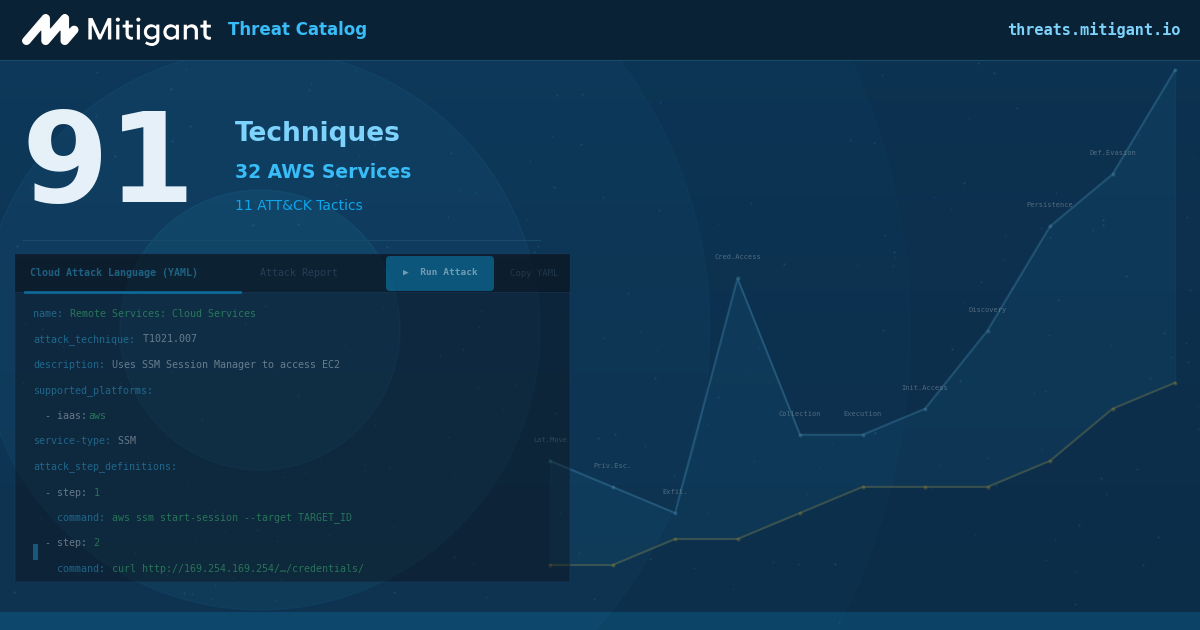
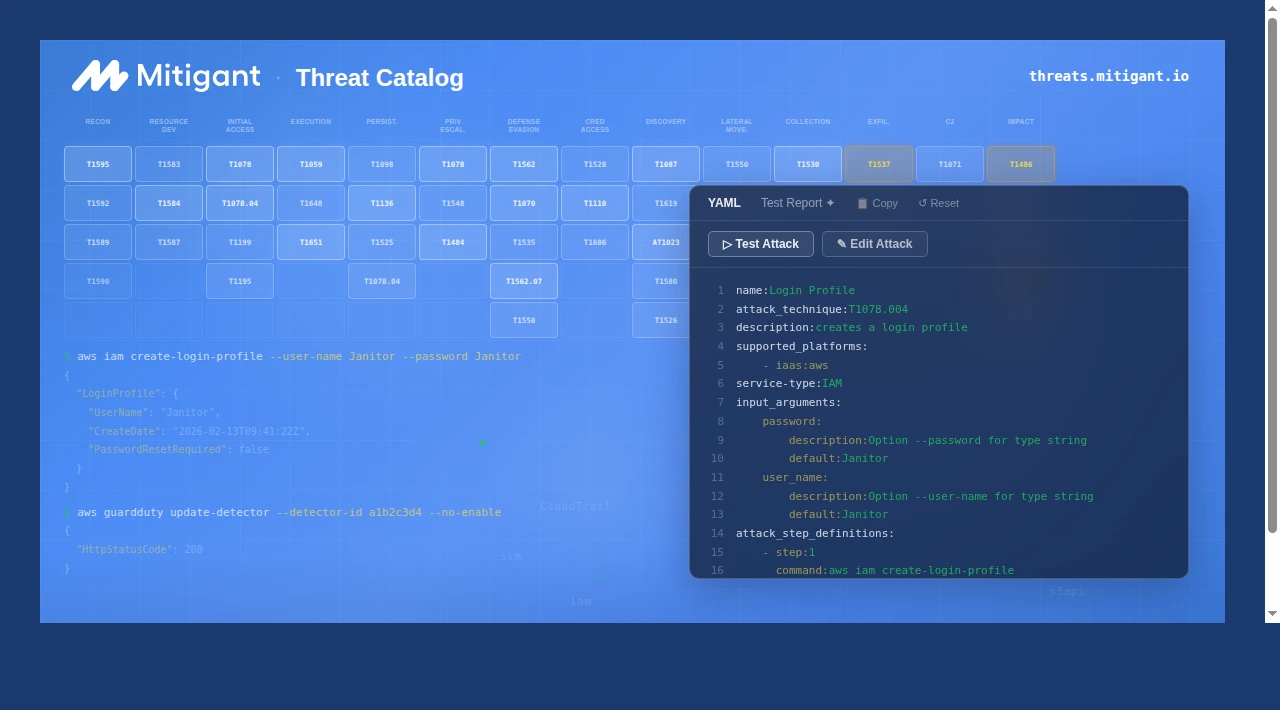
Mitigant Threat Catalog: 61 Techniques & 12 AWS Services Added
Mitigant Threat Catalog massive update! We added 61 techniques & 12 AWS services, totalling 91 techniques across 32 AWS services. The catalog now includes techniques across 11 MITRE ATT&CK tactics.
Take control of your cloud security posture
Lorem ipsum dolor sit amet consectetur. Gravida dui scelerisque magna gravida aenean purus ridiculus. Enim.
Start 30-day Free Trial








.png)