Drift-Management in der Cloud-Infrastruktur


Cloud-Drifts zu managen ist eine der Herausforderungen, vor denen Cloud-native Unternehmen stehen. Es mag zwar einfach sein, eine komplexe Cloud-Infrastruktur mit einem einzigen Befehl zu orchestrieren, aber den Überblick über diese Ressourcen zu behalten, wird schnell zu einer Hürde. Unternehmen wollen keine Gatekeeper-Strukturen implementieren, die die Agilität oft behindern. Unbeaufsichtigte Cloud-Drifts könnten zu enormen Kosten und Sicherheitsproblemen führen. Dieser Blog bietet einen Überblick über Cloud-Drifts und verschiedene Drift-Management-Techniken.
Achten Sie auf die Lücke — Wie weit ist Ihre Cloud gewandert?
Die Cloud hat Unternehmen agil gemacht; die Infrastruktur kann mit wenigen Tasten oder Befehlen schnell gestartet werden. Darüber hinaus ermöglichen Funktionen wie Autoscaling, dass die Infrastruktur als Reaktion auf den Verkehr und andere Faktoren wächst. Dies kann einem Unternehmen zwar helfen, seine Ziele zu erreichen, könnte sich aber negativ auswirken, wenn keine geeigneten Maßnahmen ergriffen werden. Das Phänomen, bei dem sich eine Cloud-Infrastruktur von ihrem geplanten oder wahrgenommenen Zustand entfernt, wird als Cloud-Drift bezeichnet.
Abweichungen in der Cloud-Infrastruktur treten auf, wenn sich Cloud-Ressourcen (einschließlich Konfigurationen) vom gewünschten Zustand entfernen. Leider spüren die meisten Unternehmen den Schmerz der Cloud-Drift, bevor sie Gegenmaßnahmen ergreifen. Darüber hinaus ist die Umsetzung von Gegenmaßnahmen ebenfalls eine Herausforderung, da sie die Agilität der Konstruktions- und Produktteams beeinträchtigen könnten.
Arten von Cloud-Drifts
Abweichungen können auf verschiedenen Ebenen der Cloud-Infrastruktur auftreten, hauptsächlich aufgrund von Ressourcen- oder Konfigurationsänderungen.
Verschiebungen bei Cloud-Ressourcen
Jedes Asset in der Cloud ist eine Ressource. Daher entsteht die Anzahl der Ressourcen in einer Cloud-Infrastruktur, wenn sich Cloud-Ressourcen und -Konfigurationen aufgrund verschiedener Faktoren, einschließlich vorsätzlicher und unbeabsichtigter Gründe, ändern. Ressourcenverschiebungen treten auf, wenn Cloud-Ressourcen erstellt, geändert oder gelöscht werden.
Abweichungen bei der Cloud-Konfiguration
Die meisten Cloud-Ressourcen verfügen über einige Konfigurationen, die für das Ausdrücken des gewünschten Verhaltens entscheidend sind, einschließlich Sicherheit, Leistung und Verfügbarkeit. Daher können Änderungen an diesen Konfigurationen in unterschiedlichem Ausmaß erhebliche Auswirkungen haben. Beispielsweise könnten Änderungen an den AWS S3-Zugriffsrichtlinien den Bucket potenziell öffentlich zugänglich machen.
Auswirkungen von Cloud-Drifts
Auswirkungen auf die Kosten
Da jedes Cloud-Asset im Wesentlichen eine Ressource ist, werden die meisten Cloud-Ressourcen von den Cloud-Anbietern über ein PAYG-Modell abgerechnet. Um die Entwicklung der Cloud-Infrastruktur im Auge zu behalten, sind daher effiziente Mechanismen erforderlich, die erkennen, wann Ressourcen orchestriert werden, um festzustellen, ob sie korrekt oder falsch eingesetzt werden.
Auswirkungen auf die Sicherheit
Change Management wurde traditionell als kritischer Aspekt einer robusten Sicherheitsarchitektur angesehen. Obwohl die Verwaltung von Infrastrukturänderungen keine zentrale Sicherheitsaufgabe ist, stellt sich heraus, dass Änderungen in der Cloud-Umgebung für die Identifizierung von Sicherheitsereignissen von entscheidender Bedeutung sind. Wie bei den meisten Ereignissen, die Warnmeldungen auslösen könnten, besteht jedoch ein erhebliches Risiko für Fehlalarme, was die Komplexität des Drift-Managements erhöht.

Lebenszyklus des Drift-Managements
Die meisten Drift-Management-Mechanismen erkennen Abweichungen, indem sie das „Versöhnmuster“ verwenden. Das Versöhnermuster ist ein Software-Engineering-Muster, das darauf abzielt, das Problem der Drifts anzugehen. Dies wird erreicht, indem zwei Zustände festgelegt werden: der gewünschte Zustand (auch als erwarteter Zustand bekannt) und der tatsächliche Zustand (auch bekannt als der Zustand der realen Welt). Der gewünschte Zustand wird bei der Orchestrierung mithilfe verschiedener Methoden, z. B. DSL oder IaC, definiert und in einer Art Datenspeicher (z. B. dateibasiert, speicherintern, Objektspeicher und RDBMS) gespeichert. Abweichungen werden identifiziert, indem der gewünschte Zustand mit dem erwarteten Zustand verglichen wird, um die Unterschiede zu berechnen, d. h. die Änderungen, die sich aus der Erstellung, Änderung oder Löschung von Cloud-Ressourcen und -Konfigurationen ergeben. Das Abgleichmuster hat vier Standardmethoden: getActual (), getExpected (), abstimmen (), und zerstören (). Diese Methoden werden zur Erkennung und Auflösung von Abweichungen verwendet. Es ist wichtig zu verstehen, dass Driftmanagement das umfassendere Konzept ist, das verschiedene Aspekte im Zusammenhang mit Wolkendriftungen zusammenfasst: Drifterkennung, Driftanalyse und Driftabgleich. Lassen Sie uns diese Aspekte kurz untersuchen:

Drift-Erkennung
Dies beinhaltet Schritte, um Abweichungen zu identifizieren und höchstwahrscheinlich einen Cloud-Administrator über CLI oder Benutzeroberflächen zu informieren. Die Erkennung von Abweichungen ist die gängigste Form des Driftmanagements. Sie deckt jedoch nur einen kleinen Teil der Auswirkungen ab, sodass andere Probleme nicht gelöst werden.
Drift-Analyse
Neben der Erkennung von Abweichungen ist es manchmal wichtig, die Grundursache von Abweichungen zu verstehen, da dies dazu beitragen kann, zukünftige Abweichungen proaktiv zu verhindern oder ein Cloud-System besser zu verstehen. Bei der Driftanalyse kommen häufig unterschiedliche Mechanismen zum Einsatz, einschließlich der Analyse von Protokollereignissen. Ein kritischerer Aspekt, der bei der Analyse von Sicherheitsereignissen, die zu einer Abweichung führen, häufig angewendet werden sollte, könnte die Identifizierung von Sicherheitslücken sein.
Drift-Auflösung
Die Driftauflösung zielt darauf ab, die Unterschiede zwischen dem erwarteten und dem tatsächlichen Zustand auszugleichen. Dies ist einer der schwierigsten Aspekte des Driftmanagements, da dabei Ressourcen gelöscht oder neu erstellt werden können.
Techniken zum Drift-Management
Drift-Management-Techniken werden in zwei Hauptkategorien unterteilt: statische und dynamische Drift-Management-Techniken. Lassen Sie uns sie kurz untersuchen.
Statisches Driftmanagement
Die beliebtesten Driftmanagement-Techniken verwenden statische Techniken, die auf IAC-Systemen basieren, z. B. Terraform. Beispielsweise zielen die Terraform-Befehle terraform refresh, terraform plan und terraform apply darauf ab, die Drift zu berechnen und den gewünschten Zustand zu aktualisieren (Terraform-Statusdateien).

Dynamisches Driftmanagement
Bei diesem Ansatz wird der gewünschte Status festgelegt, indem Cloud-Konten an einem bestimmten Punkt direkt aufgelistet und ein Status beibehalten wird. Danach kann der ermittelte Zustand mit dem tatsächlichen Zustand verglichen werden, um Abweichungen festzustellen. Dieser Ansatz ist umfassender, da es möglicherweise einige Ressourcen gibt, die nicht über IaC bereitgestellt werden und daher nicht in der Drift enthalten sind. Darüber hinaus ist der Abgleich effizienter, da er direkt durch die Nutzung der SDKs des Cloud-Anbieters erfolgt. Im Wesentlichen nutzt das dynamische Drift-Management ein Asset-Management-System oder eine CMDB, um ein detailliertes Bild des erwarteten Zustands aufrechtzuerhalten und erweiterte Abläufe wie CRUD und Versionierung zu ermöglichen. Dieser Ansatz ist auch bekannt als Infrastruktur als Software.

Statisches versus dynamisches Driftmanagement
Ähnlich wie bei anderen Rechenmechanismen gibt es eine kontinuierliche Diskussion über die Vor- und Nachteile statischer und dynamischer Driftmanagementtechniken. Eine erhebliche Einschränkung des Ansatzes zur Steuerung statischer Drift besteht darin, dass er sich ausschließlich auf die Infrastruktur beschränkt, die anhand des ermittelten Sollzustands orchestriert wird. Daher hat es keine Kenntnisse über die Infrastruktur, die auf andere Weise bereitgestellt wird, z. B. über andere IAC-Systeme. Terraform ist sich beispielsweise der Infrastruktur nicht bewusst, die auf andere Weise bereitgestellt wird, z. B. über AWS CDK, Pulumi, Cloud-APIs oder Cloud-Webkonsolen. Dynamische Drift-Management-Ansätze scannen jedoch die gesamte Cloud-Infrastruktur unabhängig von der Orchestrierungsquelle und können die Abweichungen anschließend nahtlos beheben. Dynamische Drift-Management-Systeme sind jedoch nicht einfach zu implementieren, da es sich um traditionelle Softwareanwendungen handelt und die Implementierung daher viel länger dauert. Eine Alternative ist die Verwendung verwalteter dynamischer Drift-Systeme, z. B. AWS Config.

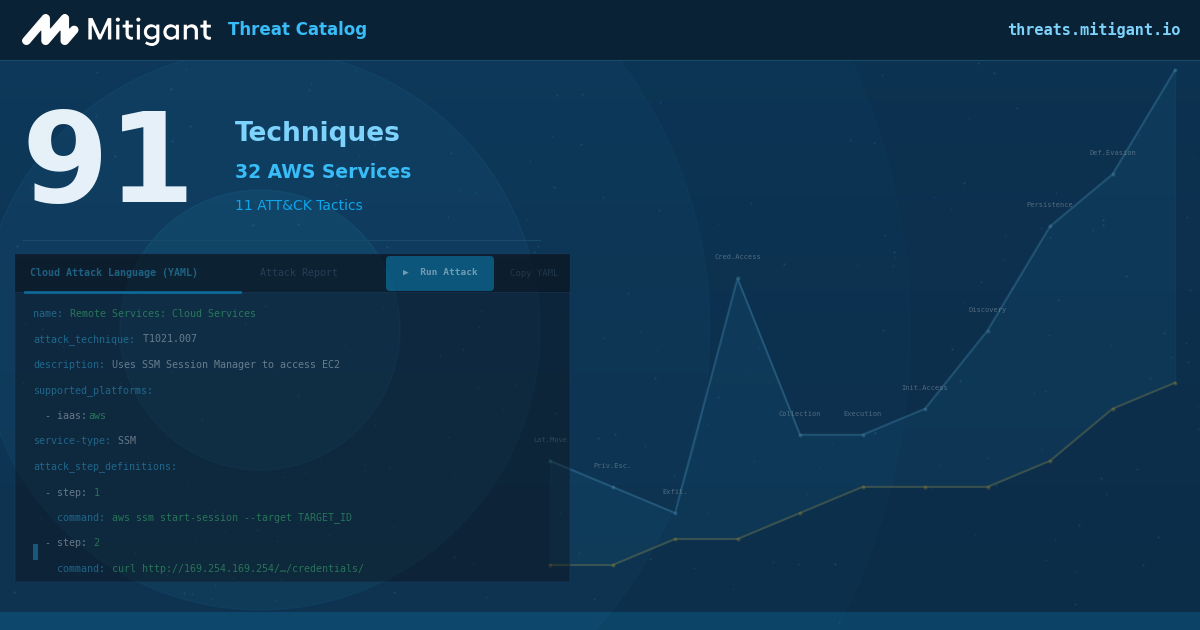
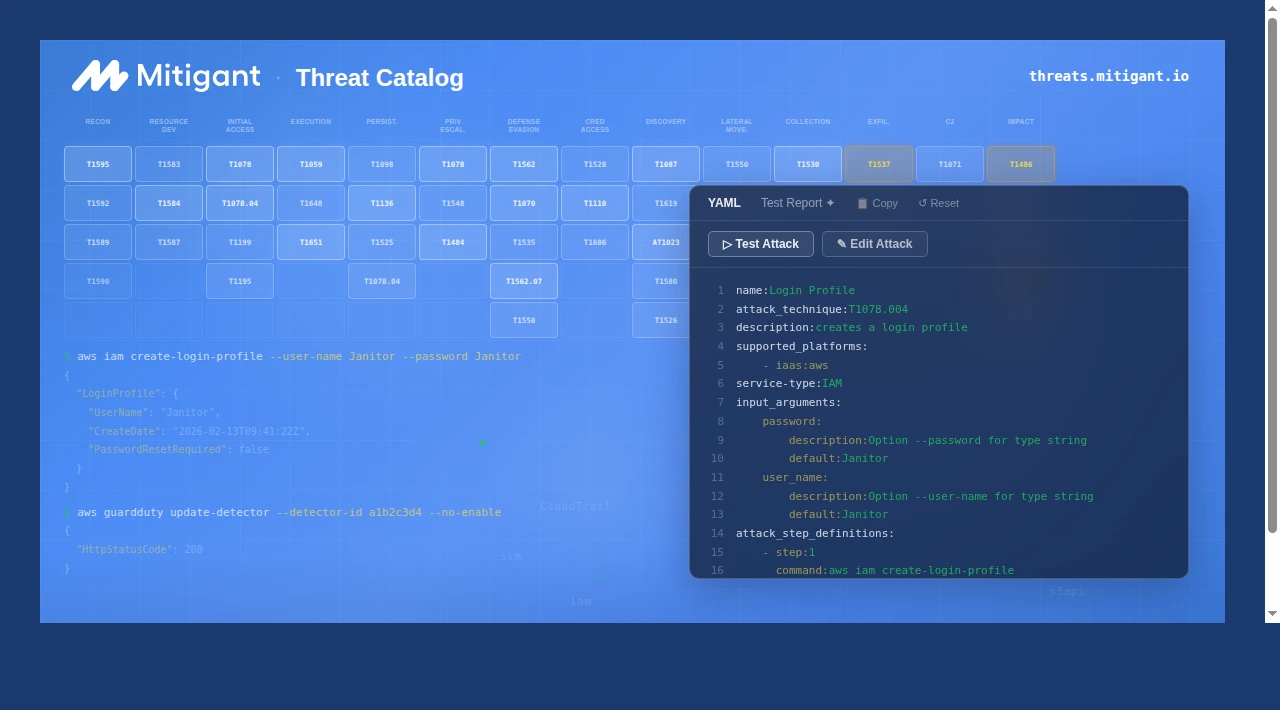
Das Drift-Managementsystem von Mitigant
Managementsystem zur Vermeidung von Abweichungen verwendet dynamische Drift-Management-Ansätze, um eine kontinuierliche Erkennung, Analyse und Auflösung von Drifts zu ermöglichen. Da es sich um eine SaaS-Plattform handelt, müssen die Entwicklungsteams keine Zeit damit verbringen, ein System zu erstellen. Stattdessen sind alle Funktionen sofort einsatzbereit. So werden beispielsweise Abweichungen in der AWS-Infrastruktur automatisch verfolgt, und es werden Benachrichtigungen gesendet, um eine schnelle Reaktion zu ermöglichen. Darüber hinaus konzentriert sich die Analyse der Mitigant-Drift auf die Untersuchung der Sicherheitsereignisse, die zu Abweichungen geführt haben könnten, sodass proaktive Gegenmaßnahmen ergriffen werden können.
Überwinde mit Mitigant ein für alle Mal den Schmerz der Wolkenverwehungen, indem du dich anmeldest hier. Wir freuen uns auch, Ihnen eine zu geben kostenlose Demo.





.png)