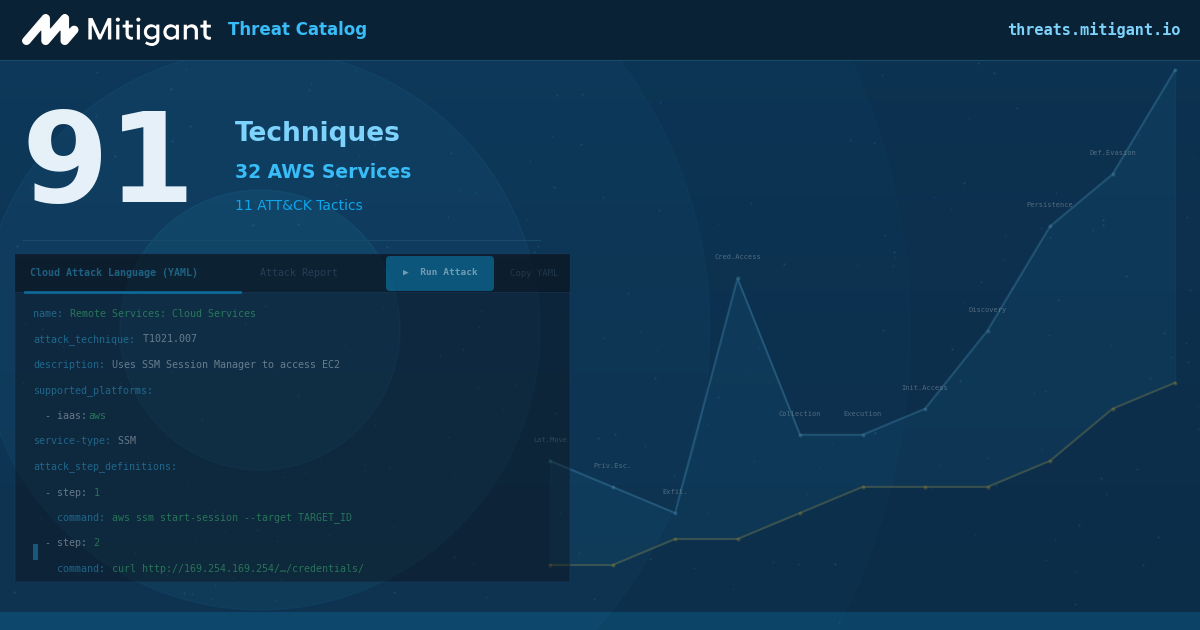
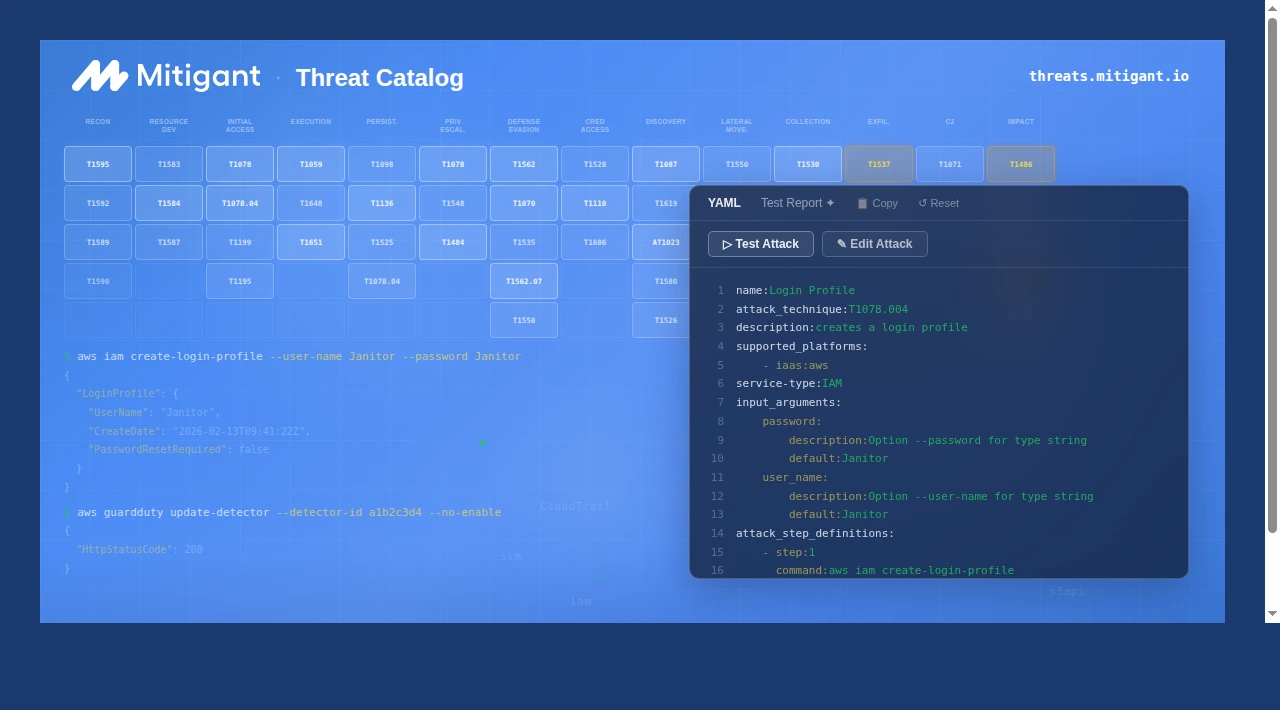
Mitigant Threat Catalog: 61 Techniques & 12 AWS Services Added
Mitigant Threat Catalog massive update! We added 61 techniques & 12 AWS services, totalling 91 techniques across 32 AWS services. The catalog now includes techniques across 11 MITRE ATT&CK tactics.
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.

Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
Join The Cloud Security Revolution Today!
Take control of your cloud security in minutes. No credit card required.






.png)